- 1 day ago Accelerating Threat Protection. Powered by Sophos Firewall’s Xstream architecture, XGS Series appliances deliver the industry’s best zero-day threat protection, identifying and stopping the most advanced known and potential threats – including ransomware.
- Sophos Intercept X is the world’s best ransomware protection. It uses behavioral analysis to stop previously unseen ransomware and boot record attacks. Intercept X secures endpoints and servers using CryptoGuard technology, which stops both local and remote unauthorized file encryption by malicious software.
Thirty years on from the world’s first attack, ransomware is stronger than ever. Cybercriminals continue to evolve their tactics and techniques, taking advantage of changes in technology and society to refine their approach.
The result: highly advanced, highly complex threats that can bring organizations to their knees. When you add together the full costs of remediation, including downtime, people time, device cost, network cost, lost opportunities and ransom paid, the final sums per victim are eye-watering.
What’s next for ransomware?
1 day ago Offensive security tools have long been used by malicious actors as well as security professionals. These commercial and open-source tools, including the modular Cobalt Strike and Metasploit toolkits, were built for penetration testing and “red team” security evaluations—but they’ve been embraced by ransomware groups for their flexibility. Sophos Customers using Intercept X and Sophos EXP products will also see this ransomware blocked by CryptoGuard. Please note that while Intercept X and EXP will block the underlying behavior and restore deleted or encrypted files in all cases we have seen, the offending ransomware splash screen and note may still appear. Endpoint Protection Best Practices to Block Ransomware A Sophos whitepaper July 2020 1 Endpoint Protection Best Practices to Block Ransomware In our survey of 5,000 IT Managers across 26 countries, 51% of respondents revealed that they were hit by ransomware in the last year. In 73% of those incidents, attackers succeeded in encrypting data.
The one thing we can be sure of is that ransomware is going to keep evolving. Here are three new areas where the tentacles of ransomware are starting to reach.
Public cloud ransomware targets and encrypts data stored in public cloud services like Amazon Web Services (AWS), Microsoft Azure (Azure) and Google Cloud Platform (GCP).
While the public cloud offers lots of advantages, confusion about security responsibilities creates gaps in protection that hackers are quick to exploit.
In addition, weak configuration and open public access to cloud resources (be that storage buckets, databases, user accounts, etc.) make it easier for criminals to breach data storage.
Service provider attacks. As technology and threats become ever more complex, companies are increasingly outsourcing their IT to specialist managed service providers (MSPs).
Cybercriminals have realized that targeting MSPs enables them to hold multiple organizations hostage with a single attack. One attack, many ransoms.
MSPs offer a level of security expertise that is hard to match in many organizations. If you use a MSP, make security one of your selection criteria. A good MSP will be happy to share how it secures both its own and its customers’ organizations.
Encryption-free attacks. The ability to encrypt files was one of the original core capabilities needed to make ransomware a viable cybercrime.
Today cybercriminals no longer need to encrypt your files to hold you hostage. Why? Because they believe you’ll pay up just to stop your data going public.
How to defend against ransomware
Adopt a three-pronged approach to minimize your risk of falling victim to an attack.

1. Threat protection that disrupts the whole attack chain.
As we saw recently with Ryuk, today’s ransomware attacks use multiple techniques and tactics, so focusing your defense on a single technology leaves you very vulnerable.
Instead, deploy a range of technologies to disrupt as many stages in the attack as possible. And integrate the public cloud into your security strategy.
2. Strong security practices.
These include:
- Use multi-factor authentication (MFA)
- Use complex passwords, managed through a password manager
- Limit access rights; give user accounts and admins only the access rights they need
- Make regular backups, and keep them offsite and offline where attackers can’t find them
- Patch early, patch often; ransomware like WannaCry relied on unpatched vulnerabilities to spread
- Lock down your RDP; turn it off if you don’t need it, use rate limiting, 2FA or a VPN if you do
- Ensure tamper protection is enabled – Ryuk and other ransomware strains attempt to disable your endpoint protection, and tamper protection is designed to prevent this from happening
3. Ongoing staff education.
People are invariably the weakest link in cybersecurity, and cybercriminals are experts at exploiting normal human behaviors for nefarious gain. Invest – and keep investing – in staff training.
Learn more
Read our new paper Ransomware: The Cyberthreat that Just Won’t Die for a deeper dive into what’s behind ransomware’s longevity, where it’s going, and how best to defend against it.
How Sophos can help
Sophos offers a range of products and services to help you protect against ransomware:
- Sophos Managed Threat Response (MTR). Many organizations don’t have the expertise, resources, or desire to monitor their network 24/7. The Sophos MTR service is a dedicated, round-the-clock team of threat hunters and response experts who constantly scan for and act on suspicious activity.
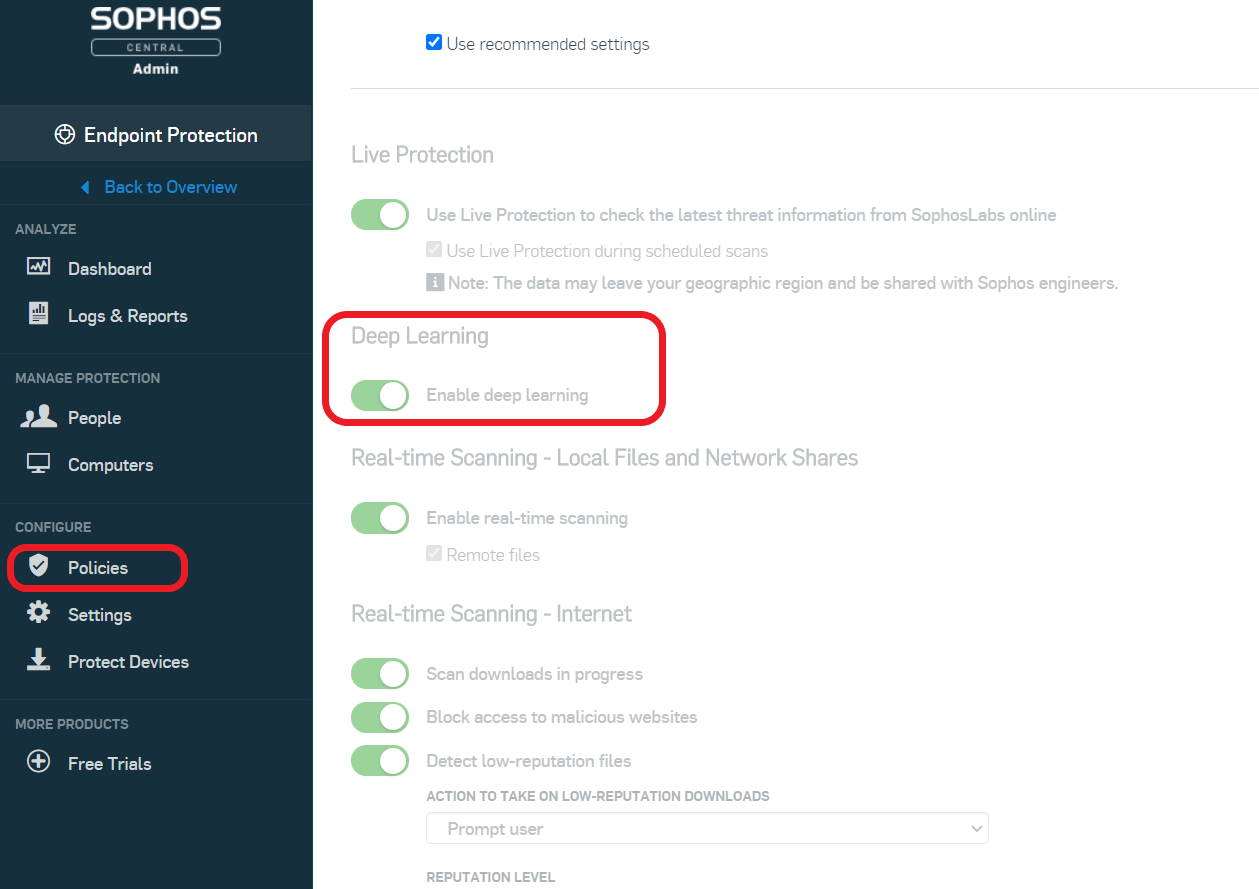
- Sophos Intercept X includes advanced protection technologies that stop ransomware on your endpoints and servers at multiple stages of the attack chain, including AI-powered threat protection, exploit protection, credential theft, deep learning and CryptoGuard.
- Sophos XG Firewall is packed with advanced protection to detect and block ransomware attacks, and stop hackers moving laterally around your network to escalate privileges.
- Cloud Optix continuously analyzes public cloud resources to detect, respond and prevent gaps in security across AWS, Azure and GCP public cloud environments that can be exploited in a ransomware attack.
- Synchronized Security. Intercept X and XG Firewall are great on their own, but even better together. If anything triggers a detection, XG Firewall and Intercept X work together to automatically isolate the affected devices – preventing the threat from spreading further.
by D. Howard Kass • Nov 23, 2020
In its newly released 2021 Threat Report, Sophos gets an early jump on forecasting cybersecurity trends it expects to see in the new year, starting with the dominant theme: Ransomware and rapidly evolving hacker tactics of all levels will shape the threat landscape and IT security in 2021.
After all, this is the time of the year that security specialists predict what’s coming in 2021 based on what’s happened in 2020, a year that many of us would like to forget. The security specialist’s report is authored by its researchers with input from its threat hunters, rapid responders, and experts in cloud security and artificial intelligence.
Here are the three major cybersecurity trends the U.K.-based company expects in 2021:
1. Ransomware:
Big-game hunting ransomware families will continue to hit larger organizations with multi-million dollar ransom demands. The number of apprentice hackers using ransomware-for-rent will increase and target high volumes of smaller prey. While cyber crews are differentiating themselves by skills and targets, ransomware families are sharing best-of-breed tools and forming “self-styled collaborative cartels,” said Chester Wisniewski, Sophos principal research scientist.
2. Commodity malware:
Everyday threats will demand “serious security attention.” Regular bugs may seem like “low level malware noise,” but they allow hackers to gain a foothold in a target. “Commodity malware can seem like a sandstorm of low-level noise clogging up the security alert system, Wisniewski said. “Any infection can lead to every infection.”
3. Detection:
All levels of hackers will “increasingly abuse legitimate tools, well known utilities and common network destinations” to skirt detection and and “stay under the radar” while they prepare to launch a network attack. “This technique challenges traditional security approaches because the appearance of known tools doesn’t automatically trigger a red flag,” said Wisniewski.
The report also examines other security trends Sophos expects to continue in 2021:
- Attacks on server platforms running both Windows and Linux to infiltrate organizations from within.
- The impact of the COVID-19 pandemic on IT security, including remote teleworkers using personal networks.
- Security challenges facing cloud environments, specifically issues different to those of a traditional enterprise network.
- Common services like RDP and VPN concentrators, which remain a focus for attacks on the network perimeter.
- Software applications engaged in tactics that are increasingly indistinguishable from overt malware.
- The reappearance of VelvetSweatshop, a default password feature for earlier versions of Microsoft Excel used to conceal macros or other malicious content in documents.
- The need to quantify unseen, undetected and unknown cyber threats to bridge gaps in detection, assess risk and define priorities.
Sophos Home Ransomware Protection
Related Content
